Customer Information on Petya Ransomware for PENTAX Medical Informatics, Speech, Voice and Swallowing Systems
Description
We recognize our Informatics, Speech, Voice and Swallowing Systems are impacted by the Petya ransomware virus. Petya is designed to spread rapidly among computers on the same network, encrypt files on the infected system, empowering the attackers to demand ransom from users to decrypt the files. Similar to the WannaCry virus, Petya uses the “EternalBlue” exploit against the Windows’ Server Message Block (SMB) protocol.
Recommendations
Those customers who installed Microsoft security patch MS17-010 are not at risk from Petya; however, for those customers who have yet to install this patch, we recommend the installation of this patch to help safeguard their PENTAX Medical systems listed below. More details and instructions are on Microsoft’s Security Bulletin at: https://technet.microsoft.com/en-us/library/security/ms17-010.aspx .
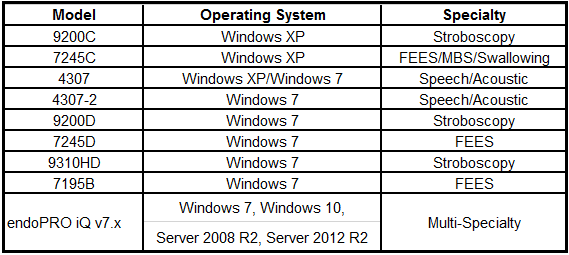
In addition, Microsoft has released new security patches via the June 2017 security update. This security update is meant to prevent other possible Windows’ exploits from occurring. These patches can be referenced in the Microsoft Security Advisory (MSA) 4025685 at: https://technet.microsoft.com/en-us/library/security/4025685.aspx . The PENTAX Medical systems listed below support the MSA 4025685 patches.
Systems that support the Microsoft Security Advisory 4025685
In case these products are operated in a stand-alone mode, there is no impact of the ransomware virus and there is no need to apply the security patch.
There is no impact on other products than the listed above in case they are operated in a stand-alone mode, but in case they are used in a network, we recommend to ensure the Windows PCs’ are updated.
If you have any questions, please contact your local PENTAX Medical representative.
Sincerely,
PENTAX Medical

